Swarm Secrets
This article refers to Platform v3.1.0. The current Platform version is v3.2.0.
Overview
Swarm secrets are Docker-native secret objects that applications create on the cluster via their docker-compose.yaml secrets: section. Services in the cluster mount them as files at a known path, with encryption at rest and in transit managed by Docker Swarm.
This card is distinct from the cluster's Global Secrets: Global Secrets are Barbara-managed key-value pairs distributed to every workload, while Swarm secrets are app-declared objects that live and die with the app that owns them.
Swarm Secrets card
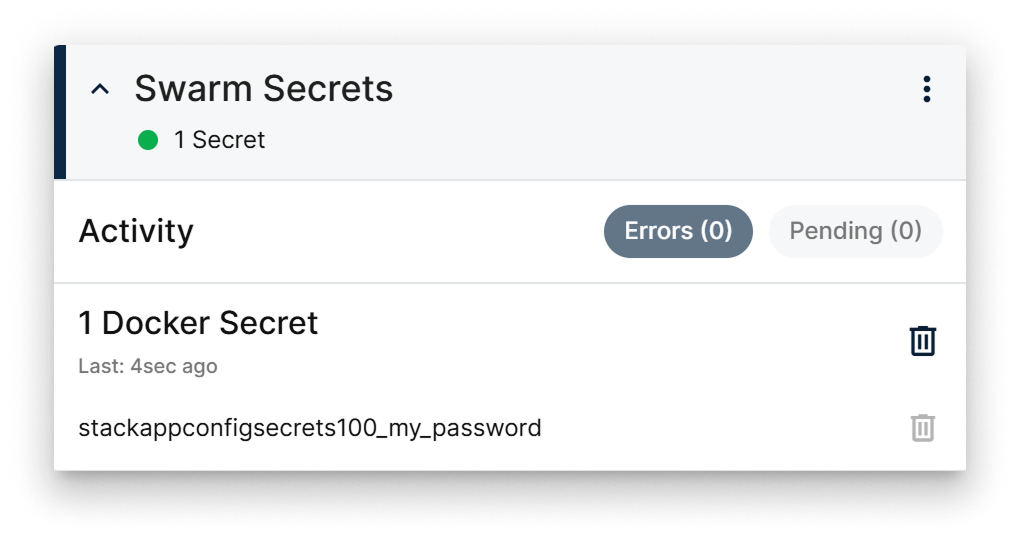
Swarm Secrets card
The card exposes:
- The list of Swarm secrets declared by the applications running on the cluster.
- Per-secret status indicators and last-activity timestamps.
- A delete action for secrets that are not in use.
Only Swarm secrets not referenced by any running service can be deleted from this card. Attempting to delete a secret in use is blocked to prevent disrupting the consuming app.
Summary
Use the Swarm Secrets card to audit the Swarm-native secrets created by your cluster apps. Use the Global Secrets card when you want Barbara to manage and distribute the secrets centrally instead.